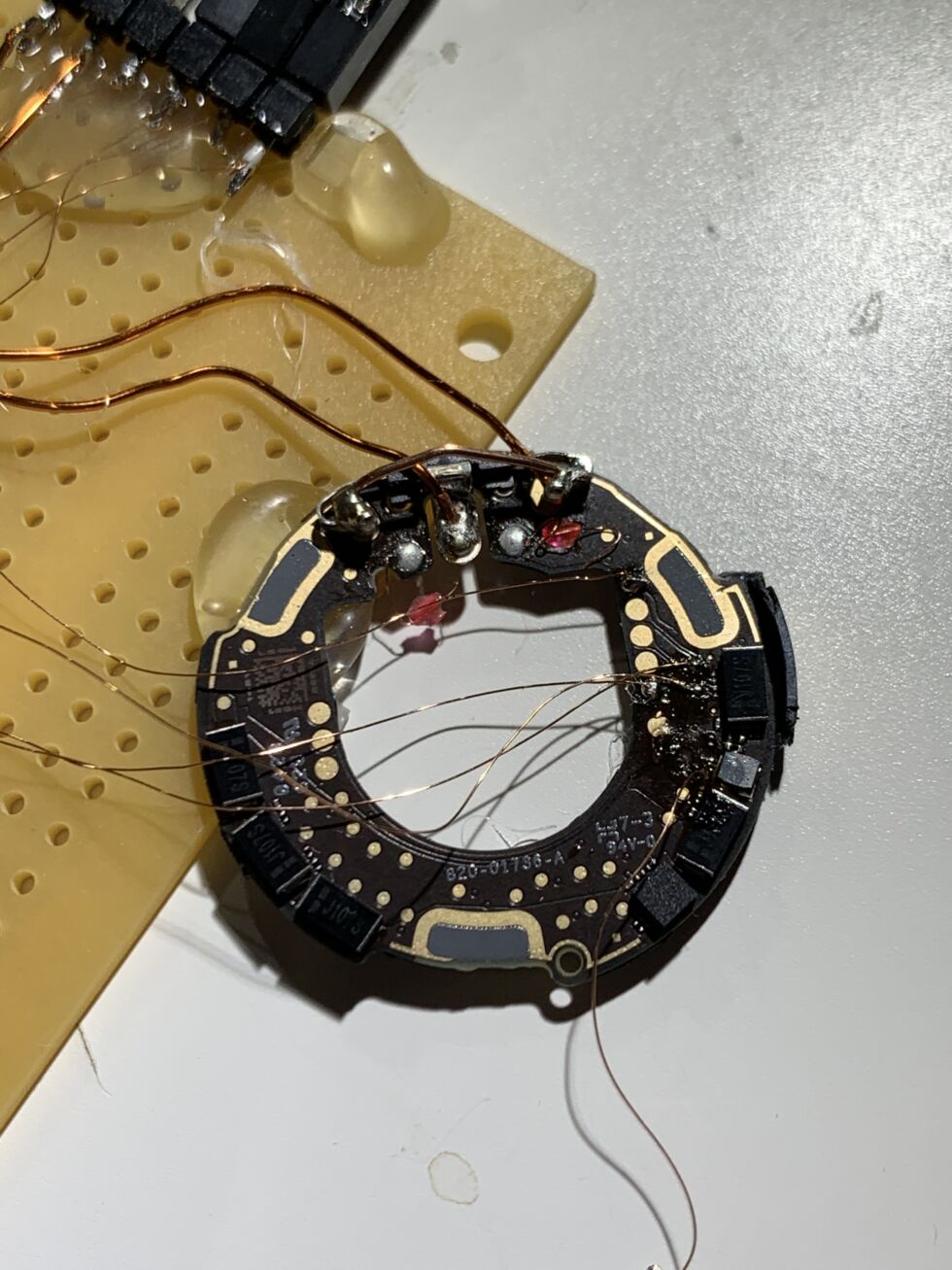
After completely bricking two AirTags, stacksmashing succeeded in breaking into and reprogramming a 3rd. [credit: stacksmashing ]
This weekend, German safety researcher stacksmashing declared success at breaking into, dumping, and reflashing the microcontroller of Apple’s new AirTag object-location product.
Breaking into the microcontroller primarily meant having the ability each to analysis how the gadgets operate (by analyzing the dumped firmware) and to reprogram them to do surprising issues. Stacksmashing demonstrated this by reprogramming an AirTag to cross a non-Apple URL whereas in Misplaced Mode.
Misplaced Mode will get a little bit extra misplaced
When an AirTag is about to Misplaced Mode, tapping any NFC-enabled smartphone to the tag brings up a notification with a hyperlink to discovered.apple.com. The hyperlink permits whoever discovered the misplaced object to contact its proprietor, hopefully ensuing within the misplaced object discovering its method house.
Learn 7 remaining paragraphs | Feedback