Researchers demonstrated on Wednesday that they’ll idiot a contemporary face recognition system into seeing somebody who isn’t there.
A staff from the cybersecurity agency McAfee arrange the assault in opposition to a facial recognition system much like these at the moment used at airports for passport verification. Through the use of machine studying, they created a picture that regarded like one individual to the human eye, however was recognized as any individual else by the face recognition algorithm—the equal of tricking the machine into permitting somebody to board a flight regardless of being on a no-fly record.
“If we go in entrance of a reside digital camera that’s utilizing facial recognition to determine and interpret who they’re taking a look at and evaluate that to a passport picture, we are able to realistically and repeatedly trigger that form of focused misclassification,” stated the research’s lead creator, Steve Povolny.
The way it works
To misdirect the algorithm, the researchers used a picture translation algorithm often known as CycleGAN, which excels at morphing pictures from one type into one other. For instance, it might probably make a photograph of a harbor look as if it had been painted by Monet, or make a photograph of mountains taken in the summertime appear like it was taken within the winter.
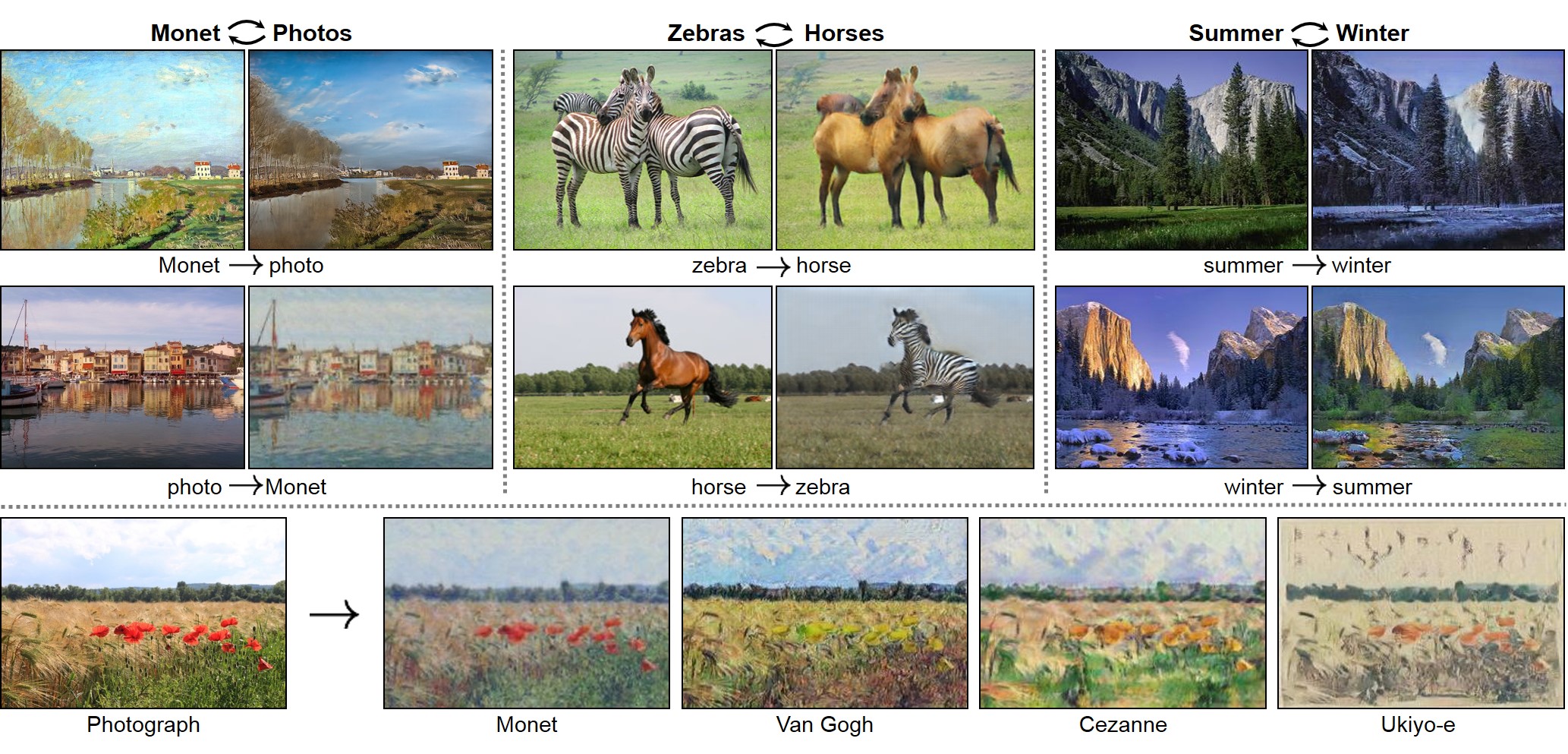
The McAfee staff used 1,500 images of every of the challenge’s two leads and fed the photographs right into a CycleGAN to morph them into each other. On the identical time, they used the facial recognition algorithm to verify the CycleGAN’s generated photos to see who it acknowledged. After producing a whole bunch of photos, the CycleGAN finally created a faked picture that regarded like individual A to the bare eye however fooled the face recognition into pondering it was individual B.

Whereas the research raises clear issues in regards to the safety of face recognition methods, there are some caveats. First, the researchers didn’t have entry to the precise system that airports use to determine passengers and as a substitute approximated it with a state-of-the-art, open-source algorithm. “I believe for an attacker that’s going to be the toughest half to beat,” Povolny says, “the place [they] don’t have entry to the goal system.” Nonetheless, given the excessive similarities throughout face recognition algorithms, he thinks it’s seemingly that the assault would work even on the precise airport system.
Second, at present such an assault requires plenty of time and assets. CycleGANs want highly effective computer systems and experience to coach and execute.
However face recognition methods and automatic passport management are more and more used for airport safety world wide, a shift that has beenaccelerated by the covid-19 pandemic and the will for touchless methods. The expertise can also be already extensively utilized by governments and companies in areas resembling regulation enforcement, hiring, and occasion safety—though many teams have referred to as for a moratorium on such developments, and a few cities have banned the expertise.
There are different technical makes an attempt to subvert face recognition. A College of Chicago staff just lately launched Fawkes, a software meant to “cloak” faces by barely altering your images on social media in order to idiot the AI methods counting on scraped databases of billions of such footage. Researchers from the AI agency Kneron additionally confirmed how masks can idiot the face recognition methods already in use world wide.
The McAfee researchers say their purpose is finally to reveal the inherent vulnerabilities in these AI methods and clarify that human beings should keep within the loop.
“AI and facial recognition are extremely highly effective instruments to help within the pipeline of figuring out and authorizing folks,” Povolny says. “However once you simply take them and blindly exchange an present system that depends completely on a human with out having some form of a secondary verify, then you definitely rapidly have launched possibly a better weak spot than you had earlier than.”